The meteoric rise of cybercrime has been unprecedented, with the world now expected to lose a staggering $10.5 trillion to attackers by 2025. Cybercriminals have no shortage of methods to choose from when looking to exploit their victims. But the most successful involves passwords. As much as 81 percent of all business data breaches are the result of poor passwords.
In particular, attackers love to use a technique called password spraying, whose success rate is surprisingly high. So, what is password spraying, and how can organizations prevent it? This guide provides an overview of this attack and the steps that users and organizations can take to protect their digital assets from a password spray attack.
Let's delve right in!

Password spraying is a type of brute force attack where adversaries attempt to gain access to multiple accounts on the same service or platform by repeatedly entering common passwords. It differs from a traditional brute force attack in that only one password is used. This technique has been popularized by attackers because it allows them to remain undetected for extended periods of time.
But what makes password spray attacks so effective? The primary reason is that most internet users prefer to use simple passwords that are easy to remember. As a matter of fact, the password "123456" is used by a shocking 23 million people.
In addition, many people reuse the same password across multiple accounts and services. Unfortunately, attackers are well aware of this fact, and they use it to their advantage by guessing common passwords with a single attack. If a criminal can gain access to even a few of your company accounts, they'll likely be able to view vital information such as financials, customer data, and more. The repercussions can be devastating.
A password spraying attack generally goes through three stages. Here's a closer look at each of them.
Stage 1: Attackers Buy or Create a List of Usernames
Before launching a password spray attack, the attacker must obtain or create a list of usernames that are linked to the target account. Attackers can go about this in many different ways. For example, they may use publicly available information, such as corporate directories, to compile their list.
Alternatively, attackers could purchase lists from underground markets. With more than 15 billion credentials currently listed for sale on the dark web, getting the information they need to launch an attack is a breeze.
Stage 2: Cybercriminals Get a List of Commonly Used Passwords
Armed with a list of usernames, the attacker will then begin to compile a list of passwords they can use together with those usernames to breach the target accounts. Unfortunately, most of the passwords used in these types of attacks are surprisingly easy to procure. Sources like Wikipedia and other reports publish thousands of common passwords. Hackers may also try to guess passwords using publicly available information about their target, such as birth dates, favorite football teams, and pet names.
Stage 3: Attackers Try the Username-Password Combinations
Finally, with a list of usernames and passwords in hand, the attacker can begin the attack. The goal is to access as many accounts as possible without raising suspicion or triggering account lockout policies. During this stage, the attacker will try each username-password combination and quickly move on to the next username if it does not work. Most attackers automate this process using custom scripts, making it even more difficult to detect. By the end of the attack, some of the accounts may have been compromised, potentially giving criminals access to sensitive company data.
Another common form of attack is credential stuffing, which relies on the fact that many individuals use identical login credentials for multiple accounts. Credential stuffing involves placing these completely validated username and password combinations, typically obtained through a data breach, into another system's access portal. This malicious technique increases the probability of bypassing authentication measures due to users reusing passwords across various platforms.
In contrast to credential stuffing, password spray attacks involve testing some common passwords across a large number of accounts.
Thus, credential stuffing involves using a single set of credentials to gain access to other systems or applications, whereas password spraying entails using common passwords for different username.
Warding off password spraying attacks is the responsibility of both the individual users and the organization as a whole. Here's a closer look at what each party can do to stay secure.
A successful breach can be catastrophic to a company. 60 percent of small businesses go out of business within six months after a security breach. They simply can't survive the legal, reputational, financial, and operational costs associated with a data breach. As such, businesses must also take proactive steps to protect against automated attacks, especially password spraying. Fortunately, there are many tools that companies can use to mitigate the risk of password spraying, including:
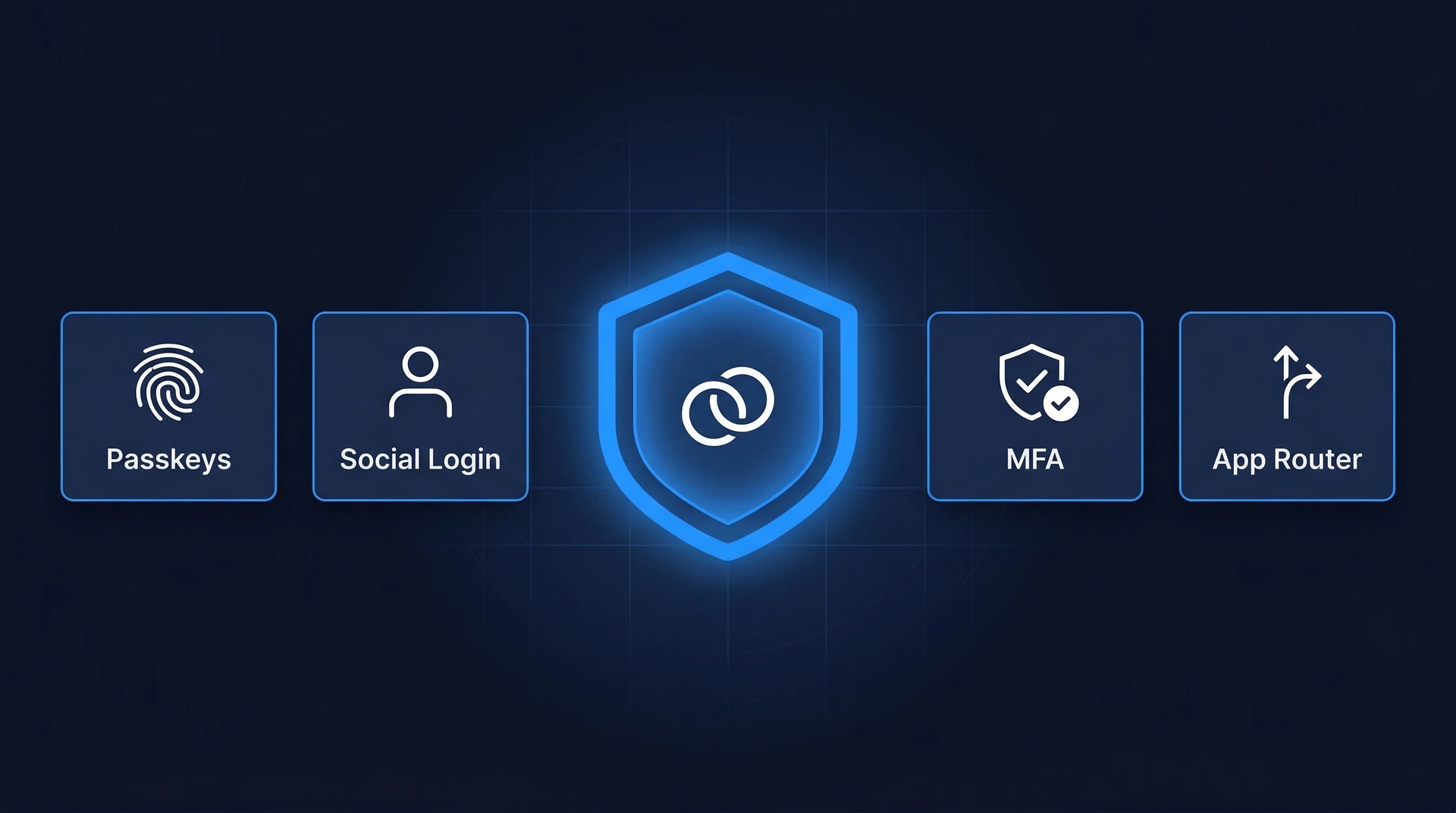
Multi-Factor Authentication (MFA)
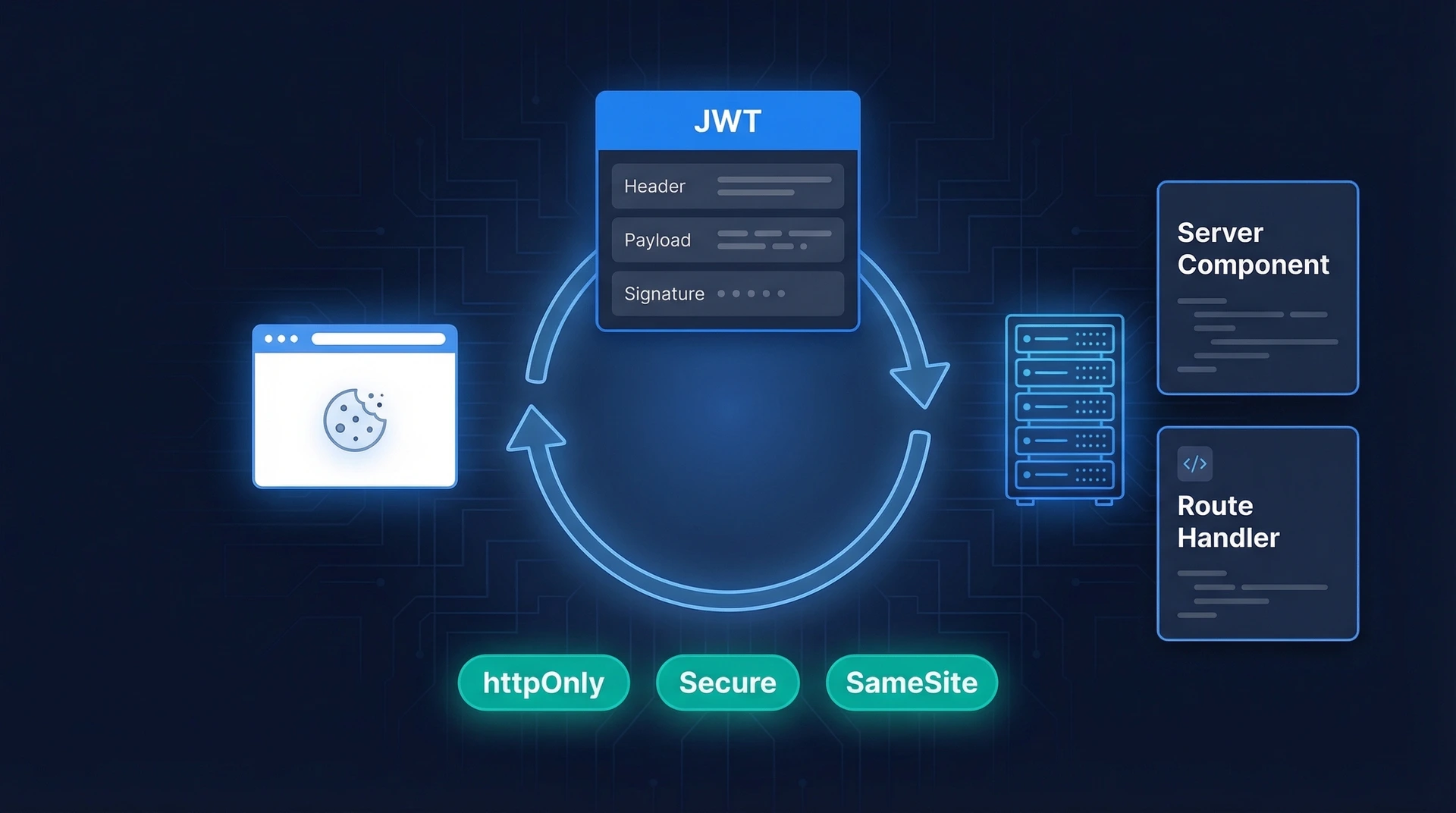
Multi-factor authentication (MFA) refers to an authentication technique whereby users are prompted to provide two or more pieces of evidence in order to verify their identity. This means that even if a criminal manages to guess the user’s login credentials, they cannot access the account without the additional security codes.

For example, MFA can require a user to first enter their username and then provide an additional layer of authentication like SMS OTP or a biometric authentication like face or fingerprint recognition.
Passkeys
Passkeys are an advanced form of authentication that allows a user to log into a web application without the need for a complex password. With a passkey, the user only needs to provide a username if they want to sign up. After this, they're authenticated through a PIN or biometric information, just like you do when unlocking your phone. This new authentication method removes the need for passwords.
Biometric Authentication
Biometric authentication relies on an individual’s physical traits, such as their fingerprints or face, to gain access to the system. It has become one of the most common method of authentication and is more secure than traditional passwords because inherence factors are very difficult to forge, making them one of the most reliable forms of authentication. In addition, biometric authentication is quick and easy to use, adding an extra layer of security without compromising the user experience.
Use a Password Manager
Unique passwords are difficult to guess or crack. A password manager can help users generate passwords to include upper case and lower case letters, special characters, and numbers. These tools are also perfect for securely storing your passwords, so you don’t have to rely on your memory.
Use Different Passwords for Different Accounts
Don’t use the same password across multiple accounts. Doing so puts the security of all your accounts at risk, as criminals can easily gain access to all of them if they manage to crack one.
Use Multi-Factor Authentication
Multi-factor authentication (MFA) requires users to provide two or more forms of identification when signing into their accounts. This ensures that even if an attacker manages to guess the user's login credentials, they cannot gain access to their account without the additional security code.
Build Your Defense Against Password Spraying Today
Password spraying can cause serious damage to companies and individuals. That's why it’s important to implement the necessary security measures to prevent it. Generally, the risks posed by successful password spraying attacks largely depend on what role the individual in your company who has been breached plays in the organization. The more privileged a user is, and the more vital the data that was accessed during the attack, the higher the risk of a successful attack becoming catastrophic to your business.
The good news is that you can protect your organization against password spraying. With Authgear, you have access to an array of highly advanced security features to protect businesses from password spraying and credential stuffing attacks. Biometric Logins, Whatsapp OTPs as MFA, and Passkey-enabled passwordless logins are some of Authgear's remarkable tools that guarantee protection against these attacks.
Get in touch with us today to find out how we can help you build a robust defense against potential threats.