Passwordless authentication includes all authentication methods that verify users’ identities without asking users to enter their passwords. Examples of passwordless authentication include biometrics, such as fingerprint and face recognition, physical security token key, magic link, etc.
Even though they are not completely safe from hacking, passwordless authentication methods are still superior over password authentication in several ways and all kinds of applications, whether commercial or enterprise, have adopted password authentication.
In this blog post, we will learn more about:

Passwords are intrinsically vulnerable to hackers for several reasons. As users register for more services online, they can easily forget their passwords, come up with simple passwords that are vulnerable to dictionary attacks, or just use the same sets of passwords for all services. Sometimes, the users might even give out their passwords willingly. Hackers can easily phish for user passwords by sending fraudulent emails or messages. According to the 2020 Verizon Data Breach Investigation Report, 81% of hacking-related breaches involved stolen passwords or weak passwords.
To better protect users’ information, factors other than the knowledge factors, which are information that users possess such as passwords, PIN, and usernames, have been used in passwordless authentication.
Different types of passwordless authentication rely on different authentication credentials or factors. These factors, namely inherence factors and possession factors, are thought to be more secure than knowledge factors since knowledge factors can be easily stolen or forgotten.
Inherence Factors
Inherence factors are factors inherent to individuals such as fingerprint, voice, and retina, and therefore users do not have to memorize them. Biometric authentication is the technology that utilizes these factors to verify a user’s identity.
When users create new accounts, their physical characteristics will be scanned and analyzed to create digital copies that will be stored in the database. When they want to log into different software or applications, the system will compare the presented physiological data with the ones stored in the database to verify their identities.
Although hackers have found their ways to spoof some of the biometric data, behavioral factors are still hard to replicate, making biometric authentication much more secure than password authentication.
Possession Factors
These are the credentials that users have with them, such as a security token or a mobile phone that can receive codes from an authentication app, OTPs through Telegram, or WhatsApp, etc. It checks if the user has the approved piece of hardware, making it much harder than the knowledge factor to crack. Nonetheless, it is still possible for hackers to gain remote access to the hardware to physically steal the hardware.
Some also argue that a few passwordless authentication, such as magic link, OTPs, and authenticator apps, are not entirely passwordless since in order to verify their identities through these methods, users still need to log into their email accounts or devices with their usernames and passwords. Nevertheless, authentication methods using possession and inherence factors are still much more secure than password authentication.

Passwordless authentication methods with biometric data or hardware keys rely on a cryptographic key pair with a public key and a private key. Despite its name, the public key actually serves as the padlock or the keyhole that is unlocked by the private key.
When a user creates a new account, a private key and its corresponding public key are generated. The public key is stored in the system on which users create their account and the private key is stored in the user’s secured device. The user can only access the private key by presenting an authentication factor, such as fingerprint, face, etc., and then the private key will be used to unlock the public key.
The “current situation will only continue to accelerate the global economic dependency on the internet” and the adoption of passwordless authentication will continue to spread according to recent studies. So, why are businesses adopting passwordless authentication as an alternative to conventional password authentication?

Provide Better User Experience
Passwordless authentication provides better user experience than password authentication since users will not have to follow complex password policies, create passwords that are too complicated to remember, and then change them from time to time as required by the applications. Furthermore, users can create new accounts or verify their identities faster with passwordless authentication without having to see the dreadful login failed messages.
Significantly Improve Data Security
Average users might experience password fatigue, which is an overwhelming feeling caused by having to memorize an excessive number of passwords and usernames, and decide to:
- Create passwords that are easy to remember
- Use the same password for all the services or apps
- Keep all the passwords in a sticky note or any unsecured place
These scenarios make it easier for hackers to guess or steal credentials and have access to sensitive information.
On the other hand, users do not have to worry about remembering hundreds of passwords with passwordless authentication since they can log in to apps through different hardware or what they were born with. Furthermore, the credentials used for passwordless authentication, such as biometric data, possession factors, and magic links, are harder for hackers to replicate or spoof and they are usually secured and encrypted on a user’s device or a FIDO security key.
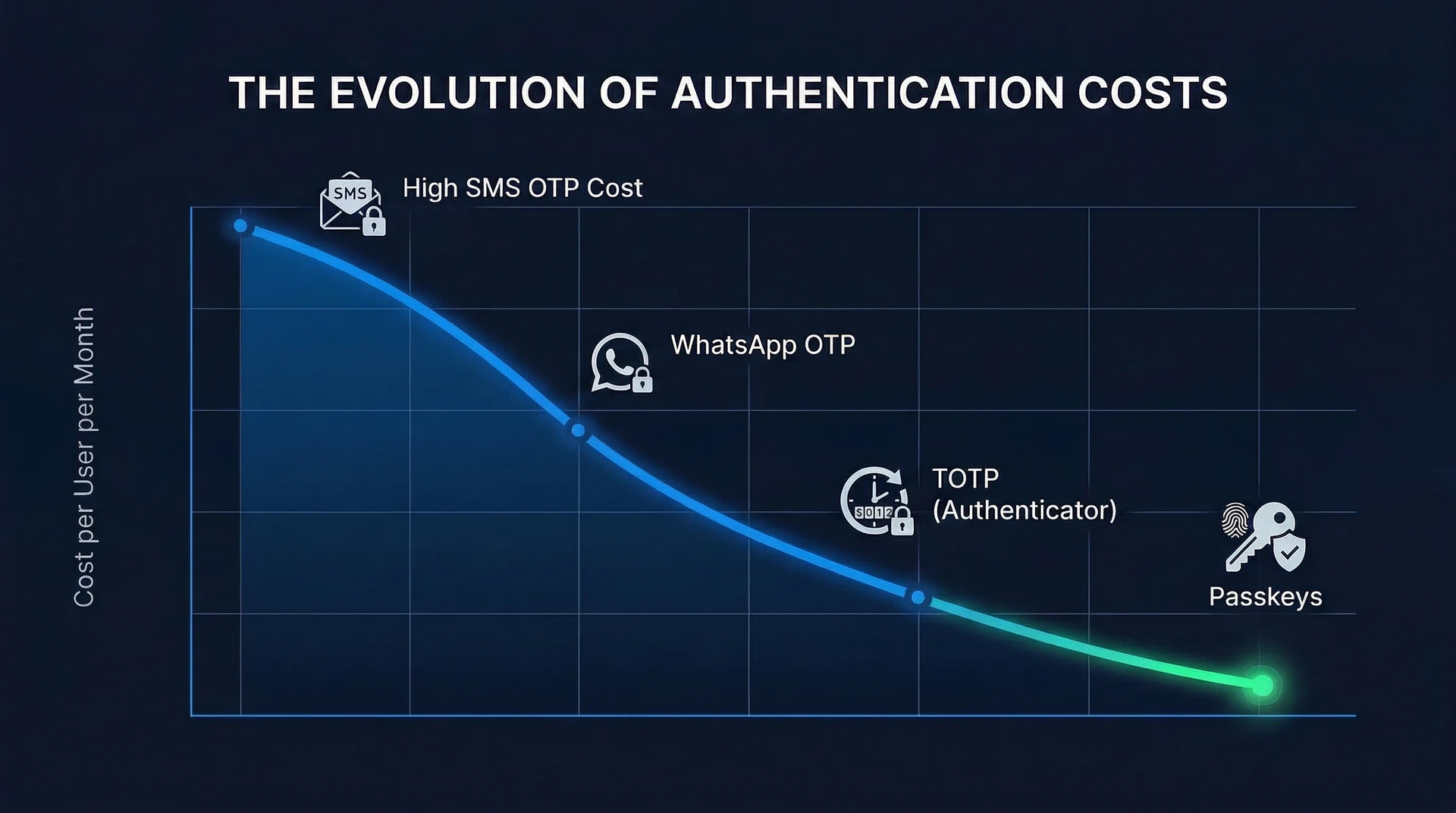
Reduce IT and Operational Costs
Resetting and managing passwords are actually more expensive than people think. A study conducted by Secret Double Octopus and Ponemon Institute suggests that passwordless authentication manages to save an average of $534K in password-related support costs and an additional $1.4M in costs over the traditional username and password authentication in the span of two years.
Keeping a password authentication system means that an enterprise needs to invest in a help desk ticketing system, recruit staff to reset passwords for users, maintain the security of the authentication system, and purchase hardware needed for the system. By eliminating passwords, companies can save millions of dollars in the long run while benefiting from the other characteristics of passwordless authentication.
The term multi-factor authentication (MFA) is different from passwordless authentication since it mainly describes the authentication process using more than one authentication factor to verify a user’s identity. For example, when you log into Gmail or Facebook now, you have to confirm that it’s you logging in to the services with an authenticator app aside from entering your username and password. In this case, you are presenting two authentication factors, one knowledge factor and one possession factor. Having more than one authentication factor strengthens the security of authentication as attackers will not only have to get the right combination of username and password but also either gain access to users’ devices or manage to spoof their biometric data.
Passwordless authentication, on the other hand, mainly describes authentication methods that do not require users to enter their passwords to log in to apps or systems. Many apps now implement both multi-factor and passwordless authentication to enhance authentication security.
Before you start implementing passwordless authentication, there are a few decisions that you have to make:
1. How many authentication factors will you include?
Using one authentication factor is certainly not recommended as it will increase the chance of data breach.
2. What method(s) of passwordless authentication will you use?
As mentioned above, there are several methods of passwordless authentication, ranging from fingerprint scan, face scan, OTP via SMS, etc., for you to choose.
From then, you can start developing your own passwordless authentication system.
Easily Implement Passwordless Authentication with Authgear
Developing and maintaining an authentication system in-house can be quite time-consuming and exhausting. Authgear provides various security features, such as SSO, social login, passwordless authentication, 2FA, and more, for your applications to provide better security and smoother user experience. Furthermore, by integrating your apps with Authgear, your apps will also be equipped with other features, such as signup page and admin portals, that help you optimize conversion rate and better manage your users.
Contact us now for us to learn more about your needs and how Authgear can help you.