When it comes to ensuring data security, it’s easy to mixed up authentication and authorization. Simply put, authentication is the process of verifying a user’s identity and confirming, through various methods, that they are who they say they are. Authorization follows on from this step but operates quite differently as it grants access to different resources based on a user’s exact level of authorization.
The difference between authentication and authorization isn’t complicated but understanding these processes makes it far easier to make informed decisions regarding data and cybersecurity systems. In this article we’re looking into just what makes authentication and authorization distinct and some examples of how they operate.
Authentication is all about checking the authenticity of the identity you’ve presented to a security system. Think about it like when you’re going through security at the airport, the first thing that gets checked is your face against the one in your ID. Authentication works similarly, the only difference is that instead of presenting an ID, you’re likely going to be asked for a password or your fingerprint to be scanned. The authentication software will then use the credentials you’ve provided and check them against the information stored in the database for verification.
Now that your identity has been verified, the next question is: what exactly are you authorized to access? To continue with the travel analogy, this would be the part where airport security would check your nationality and visa i.e. whether you have permission to enter the country.
Most data systems work similarly in that there are certain borders or levels of access that only privileged personnel can be admitted into. These separate, at the very least, basic users from those who have admin access. Once your identity is confirmed, authorization is used to confirm which resources or apps you’re approved to access based on pre-set rules.
Because authentication and authorization generally work synergistically in security systems, it’s easy to get them muddled. The important thing to note is that authentication generally needs to occur before authorization because in order to judge whether a user has permission to access things, their identity first has to be verified. For example, if you’re logging into a company database, the system needs to confirm who you are before it can determine which documents you have the authority to open.
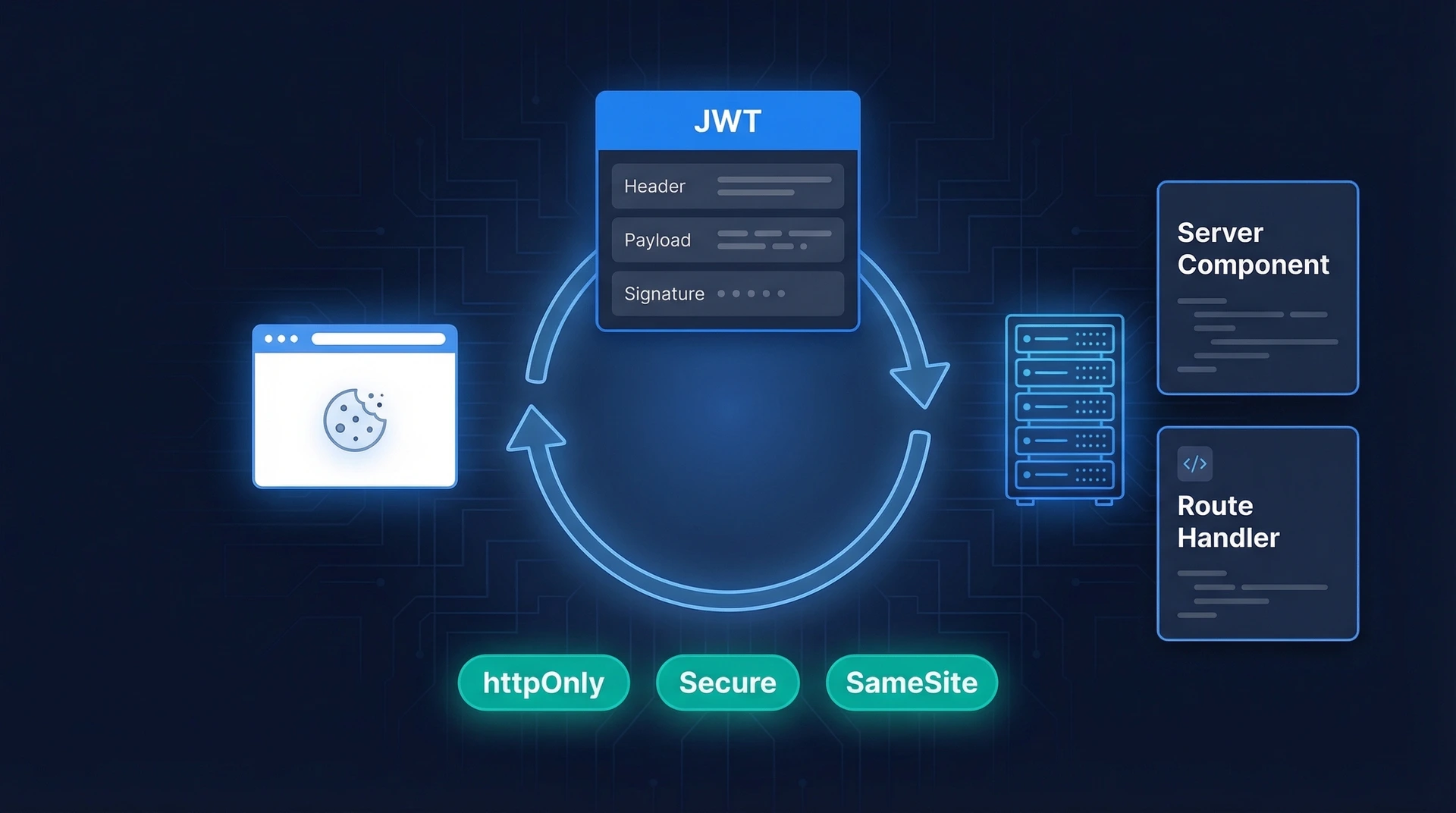
From a more technical angle, the difference between authentication and authorization is that authentication data is generally transmitted by ID tokens while authorization information is done via access tokens.
Besides performing different functions, there are also significant differences in how authentication vs authorization operates. Authentication is usually visible to the user, be it in the way they put in their password or biometrics, while authentication usually is not. This is because authorization is established by the company or host of the platform being used. It’s their pre-set settings that determine, away from the gaze of the user, whether they’ll be allowed access to certain aspects.
Unlike authorization, authentication can also be managed by the user. Options are often provided that allow users to choose the authentication method they’d prefer, be it passwords or an OTP, while authorization again falls outside of the user’s control.
If you take anything away from all of this, it’s simply that authentication and authorization cover two very distinct aspects of data security. Both of these steps, verifying identity and then access, are highly important and can’t replace the job of the other.

Most businesses these days are opting to use multi-factor authentication (MFA) for stronger protection against cyber security threats.
Authentication requires users to present certain authentication factor to verify their identity. The three main forms of authentication are inheritance, possession, and knowledge, with each relying on something from the user to verify their identity:
This type of authentication relies on things that a user knows to confirm that they are who they say they are. The most common example of this is a username and password. Other common knowledge factors include security questions and pins. Knowledge factors are considered the least secure since they can be easily guessed or stolen.
The simplest example of a possession authentication factor is your front door key – you must have it with you to gain entry into your home. There are various other forms that this kind of authentication factor can come in, be it through physical security items such as fobs or cards, or items you receive on a device such as WhatsApp OTPs and SMS OTPs.
This one may sound a little ominous but “inheritance authentication factors” is just a big title for the biometric authentication that many of us use every day when we scan our faces or fingerprints to access our phones. Whether it’s your face, retina or fingerprints scanned, this authentication factor relies on what you are in terms of your physical or biometric data to authenticate you.
Where to Begin
When it comes to authentication vs authorization, they’re both crucial parts of a data security system. There is no special level access, however, that can get around the simple fact that most software or applications need to start with some aspect of identity verification before anything else. That’s the key difference between the two tools.