Authentication is a key part of modern software. Whenever someone logs in, uses an API, or performs an action in an app, the system must confirm who they are and what they're allowed to do. In distributed systems where multiple services communicate, this process needs to be fast, dependable, and secure.
JSON Web Tokens (JWTs) are widely used for authentication and authorization because they let systems verify requests without relying on centralized session storage. They're common in APIs, microservices, mobile apps, and single sign-on setups.
However, while JWTs improve performance and scalability, they also bring security responsibilities. Most real-world issues happen not because JWTs are flawed, but because they're implemented incorrectly or without proper safeguards.
This guide explains JWT security in simple, practical language, covering how they work, why they matter, potential risks, and best practices for using them safely in production.
Why JWT Security Matters
In traditional web applications, authentication often relies on server-side sessions. The server stores session data and checks it whenever a request arrives. This approach works well for simple architectures but can become difficult to scale when systems grow or distribute across regions and services.
JWTs solve this problem by allowing identity information to be stored inside the token itself. Each service can verify the token independently, without contacting a central database. This improves performance, reduces latency, and simplifies scaling.
However, this design also changes the security model. Once a token is issued:
- It acts as proof of identity
- Any system that trusts the issuer may accept it
- Whoever holds the token can use it
If a token is leaked, copied, or forged, it can grant unauthorized access until it expires or is revoked. Because of this, protecting JWTs is as important as protecting passwords or API keys.
What Is a JWT?
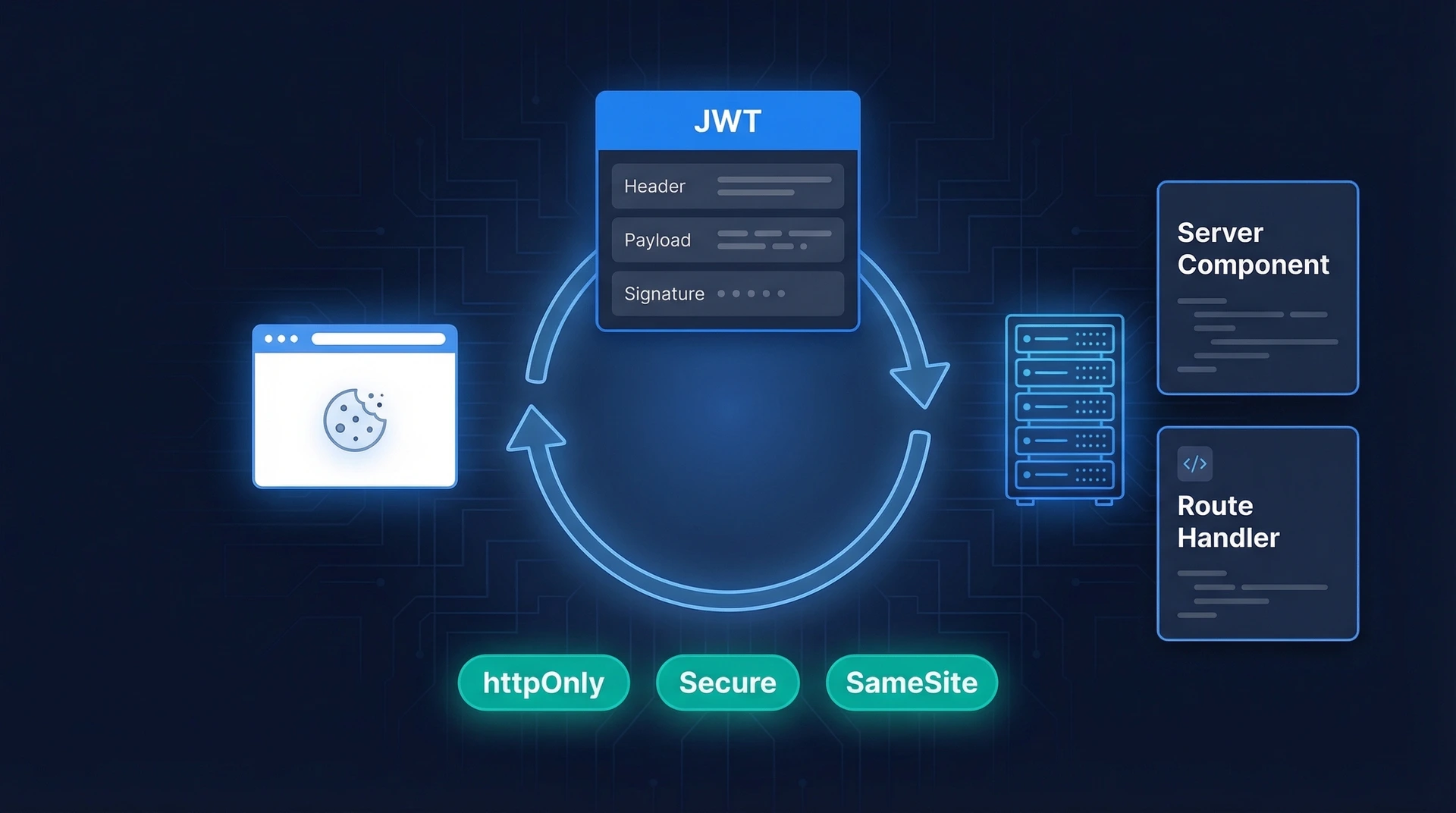
A JSON Web Token is a compact string used to securely transmit information between parties. It is made of three parts separated by dots:
- Header – Contains metadata such as the signing algorithm
- Payload – Contains claims (for example user ID or role)
- Signature – Verifies authenticity and integrity
A typical token looks like this:
xxxxx.yyyyy.zzzzz
Each part is Base64Url-encoded. Here is an example of a decoded JWT header and payload:
// Header
{
"alg": "RS256",
"typ": "JWT"
}
// Payload
{
"sub": "user_123",
"iss": "https://auth.example.com",
"aud": "https://api.example.com",
"exp": 1740000000,
"iat": 1739996400
}
The signature ensures the token has not been modified. When a server receives a JWT, it verifies the signature before trusting the payload. If the signature is invalid, the token is rejected.
JWTs are usually issued after a successful login. Instead of sending credentials repeatedly, the client sends the token with each request. The server checks the token and allows access if it is valid.
How JWT Authentication Works
A standard JWT authentication flow is simple:
- User logs in with credentials
- Server verifies credentials
- Server generates and signs a token
- Client stores the token
- Client sends token with each request
- Server validates token
Once issued, the token becomes the user's identity credential. This means security depends heavily on how tokens are generated, validated, stored, and transmitted.
Core Security Requirements for JWT Systems
A secure JWT implementation must satisfy several practical requirements:
- Tokens must be impossible to forge
- Signatures must be verified correctly
- Expired tokens must be rejected
- Tokens must only be accepted by intended systems
- Tokens must be protected during storage and transit
- Compromised tokens must be revocable
These requirements form the baseline for secure token-based authentication. If any are ignored, vulnerabilities can appear even if the token format is correct.
Common JWT Vulnerabilities
Most JWT security failures occur because of implementation mistakes. Understanding these risks helps teams design safer systems from the start.
Algorithm Misconfiguration
JWT headers specify which algorithm was used to sign the token. If a system accepts unexpected or insecure algorithms, attackers may manipulate tokens.
One well-known example is accepting tokens signed with "none". This value means no signature is present. If validation logic accepts such tokens, attackers can create fake tokens with any data they choose.
Weak Signing Keys
Tokens signed with weak secrets can be cracked through brute force or guessing. Once an attacker discovers the key, they can generate valid tokens for any user.
Weak keys often result from:
- Simple passwords
- Short strings
- Reused test keys
- Hardcoded secrets
Strong cryptographic keys are essential for preventing forgery.
Missing Claim Validation
JWT payloads contain standard claims that help validate authenticity and context. Common claims include:
- Expiration time (
exp) - Issuer (
iss) - Audience (
aud)
If a system does not check these fields, it may accept tokens that are expired, issued by unknown sources, or intended for another service.
Long Token Lifetimes
Tokens that remain valid for long periods increase risk. If a token is stolen, it can be used until it expires. Long-lived tokens extend the attack window. Short-lived tokens reduce risk by limiting how long a compromised credential can be used.
Insecure Storage
Tokens stored in unsafe locations can be stolen. For example:
- Browser local storage accessible to scripts
- Logs that capture headers
- URLs containing tokens
Attackers who gain access to storage can reuse tokens to impersonate users.
No Revocation Strategy
Because JWTs are stateless, servers do not automatically track issued tokens. Without a revocation mechanism, tokens remain valid until expiration even if:
- A user logs out
- Credentials change
- An account is compromised
Systems handling sensitive data should always include a way to invalidate tokens.
Sensitive Data in Payload
JWT payloads are encoded, not encrypted. Anyone can decode them. If confidential data is stored inside a token, it becomes visible to anyone who obtains it. Tokens should only contain information that is safe to expose if decoded.
JWT Security Best Practices
Following proven best practices helps prevent most JWT vulnerabilities. These recommendations are widely accepted across production systems.
Restrict Allowed Algorithms
Always configure validation logic to accept only approved algorithms. Tokens using unexpected algorithms should be rejected immediately. Explicit algorithm allowlists prevent attackers from manipulating headers.
Use Strong Signing Keys
Signing keys should be:
- Long
- Random
- Securely generated
They should never be stored directly in code. Instead, use secure configuration systems or secret managers.
Validate Every Claim
Every token should be checked for:
- Signature validity
- Expiration time
- Issuer identity
- Audience value
Skipping validation steps is one of the most common causes of security issues.
Keep Tokens Short-Lived
Short expiration times reduce exposure if a token is stolen. Many systems use two token types:
- Access tokens: short lifespan (e.g., 15–60 minutes)
- Refresh tokens: longer lifespan (e.g., days or weeks)
This approach balances convenience and security.
Always Use HTTPS
Tokens must always be transmitted over encrypted connections. Sending them over unencrypted networks allows attackers to intercept them. Transport encryption protects tokens during transmission.
Store Tokens Securely
Safe storage depends on platform:
- Web apps — HTTP-only cookies
- Mobile apps — secure device storage
- Servers — memory or protected stores
Avoid storing tokens where scripts or unauthorized processes can access them.
Plan for Revocation
Even stateless authentication systems need revocation strategies. Common approaches include:
- Token blacklists
- Token version numbers
- Signing key rotation
Revocation ensures access can be removed when necessary.
Avoid Sensitive Payload Data
Only include essential identity information in tokens. Do not store passwords, secrets, or personal data in payloads. Keeping tokens minimal reduces impact if they are exposed.
Signing Methods: Symmetric vs Asymmetric
JWTs can be signed using two main approaches, and choosing the right one affects both security and scalability.
Symmetric Signing
This method uses a shared secret for both signing and verification.
Advantages:
- Simple setup
- Fast performance
Limitations:
- Secret must be shared securely
- Harder to manage across multiple services
Asymmetric Signing
This method uses a private key to sign and a public key to verify.
Advantages:
- More secure in distributed systems
- No shared secret required
- Easier key rotation
Limitations:
- Slightly more complex configuration
For multi-service environments, asymmetric signing is often preferred because it limits exposure of signing keys.
Observability Benefits
JWTs can also support operational visibility. When designed carefully, they help engineers:
- Trace requests across services
- Correlate logs
- Identify unusual access patterns
- Debug authentication failures
Instead of being opaque credentials, tokens can become useful diagnostic tools.
When JWT Is the Right Choice
JWTs work especially well in systems that require:
- Stateless authentication
- Horizontal scaling
- Distributed services
- Cross-platform clients
They are commonly used for APIs, microservices, mobile apps, and federated login systems.
When JWT May Not Be Ideal
JWTs are not always the best option. Traditional sessions may be preferable when:
- Immediate revocation is critical
- Strict centralized control is required
- Security policies demand server tracking
- Token size must remain small
Choosing JWT should be a deliberate architectural decision based on system needs.
Designing Secure JWT Systems
Building a secure JWT system involves more than generating tokens. It requires coordinated decisions across architecture, infrastructure, and operations.
Teams should evaluate:
- Threat models
- Compliance requirements
- Infrastructure scale
- Operational maturity
Addressing these early ensures authentication systems remain reliable as they grow.
Practical JWT Security Checklist
A simple checklist can help verify whether a system follows best practices:
- Strong signing keys are used
- Allowed algorithms are restricted
- Claims are fully validated
- Tokens expire quickly
- Tokens are stored securely
- Sensitive data is excluded
- Revocation is supported
- Keys are rotated regularly
Systems that meet these criteria are significantly less likely to experience token-related security issues.
Bottom Line
JWTs play an important role in modern authentication systems. They support scalable identity verification, reduce server dependency on session storage, and work efficiently across distributed environments. When used correctly, they provide a reliable balance of performance and security.
Most JWT risks don't come from the technology itself, but from implementation gaps such as weak validation, improper storage, or overly long token lifetimes. Applying strong signing methods, validating tokens carefully, and enforcing strict expiration policies can significantly reduce these risks.
Making JWT security a deliberate architectural decision helps ensure your authentication system stays stable, scalable, and secure as it grows.
For teams looking to implement JWT securely and confidently, Authgear offers practical authentication tools that simplify token management, strengthen validation, and help build production-ready identity systems from the start.
Explore Authgear's JWT tools to generate secure tokens, validate signatures correctly, and implement authentication flows designed to scale safely from day one.
FAQs
What is the biggest JWT security risk?
The most common risk is improper validation. If a system fails to verify signatures, expiration times, or issuers, it may accept forged or expired tokens, allowing unauthorized access.
Are JWTs secure by default?
JWTs are secure when implemented correctly. Their safety depends on strong keys, proper validation, secure storage, and correct configuration. Weak implementations introduce vulnerabilities.
Should JWT payloads be encrypted?
Encryption is only necessary if sensitive data is included. In most systems, it is safer to avoid storing confidential information inside tokens at all.
How often should signing keys be rotated?
Keys should be rotated regularly according to security policy or risk level. Rotation limits damage if a key is exposed and is considered a standard best practice.