Two Popular Choices for Next.js Authentication in 2026
If you're building a Next.js app and researching authentication, you've probably landed on two very different options: Supabase Auth and Authgear. Both are production-ready, both work well with Next.js App Router, and both have free tiers. But they take fundamentally different approaches to authentication — and that difference matters a lot depending on your stack.
This guide is a fair, practical comparison for developers choosing between Supabase Auth and Authgear for a Next.js project. No winner declared upfront — the right choice depends on what you're building. If you want a broader overview of all Next.js auth approaches first, see our Next.js authentication guide, then come back here for this specific comparison.
Quick Overview
What Is Supabase Auth?
Supabase is an open-source Firebase alternative that bundles a managed Postgres database, real-time subscriptions, file storage, and authentication in one platform. Supabase Auth is the authentication layer built into that platform. It's not a standalone product — it's designed to work alongside Supabase's Postgres database via Row Level Security (RLS) policies.
If you're already on Supabase for your database, auth is essentially included. The user table lives in your Postgres instance, and you can write RLS policies that reference auth.uid() directly in SQL to control data access per user.
What Is Authgear?
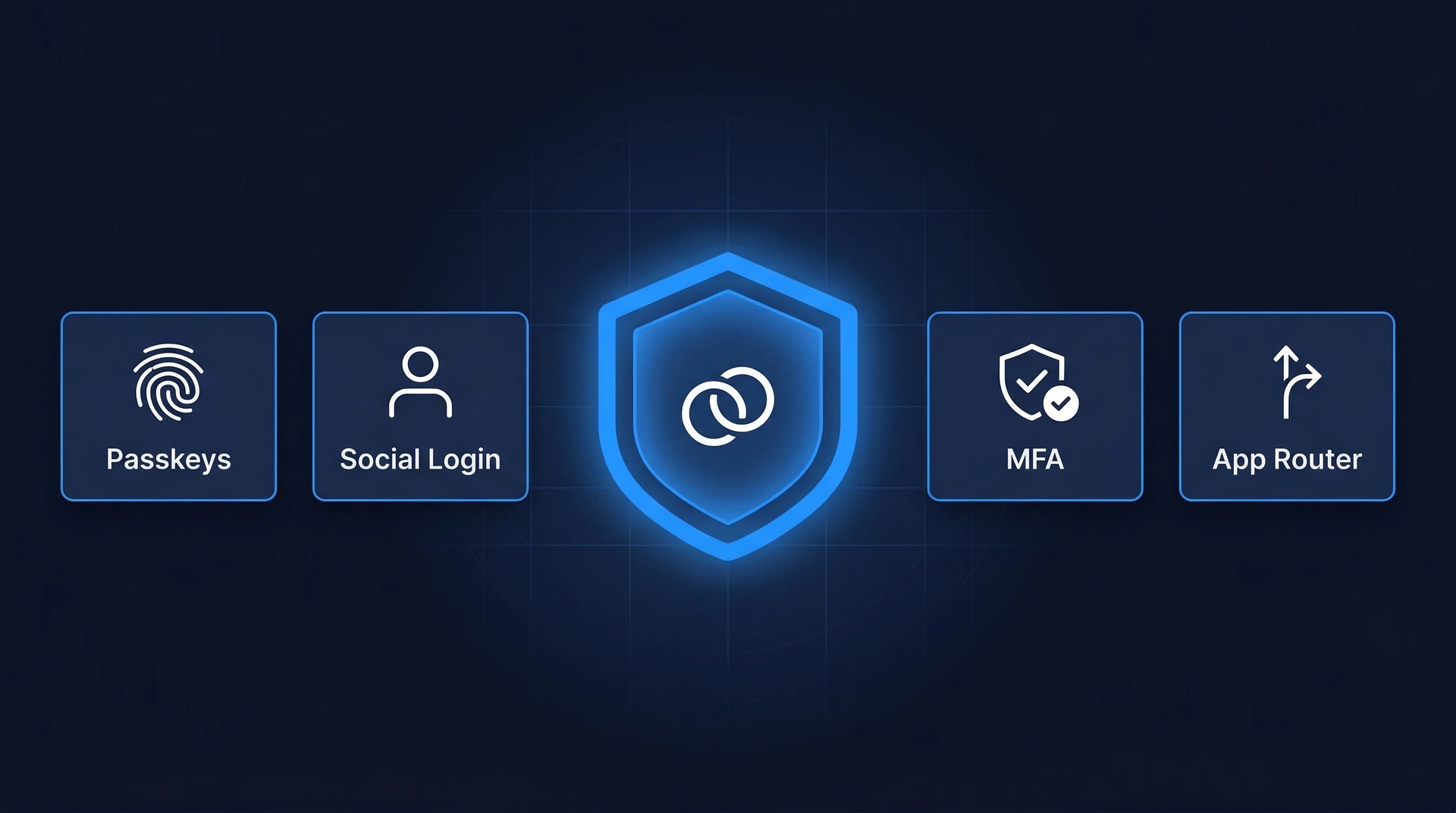
Authgear is a dedicated Customer Identity and Access Management (CIAM) platform. It does one thing — authentication and identity management — and goes deep on it. Think of it as a specialist rather than a generalist: it doesn't include a database or file storage, but it offers a richer set of auth features than most bundled solutions.
Authgear is built on open standards (OpenID Connect, OAuth 2.0, SAML), includes a pre-built customisable login UI, and ships enterprise features like SAML SSO, passkeys, fraud protection, and multi-tenant B2B support out of the box. The @authgear/nextjs SDK was built specifically for Next.js App Router.
Feature Comparison
| Feature |
Supabase Auth |
Authgear |
| Passkeys (WebAuthn) |
Not supported (as of March 2026) |
Supported — dedicated passkey flows with device sync |
| Social Login (Google, GitHub, etc.) |
Yes — 20+ OAuth providers |
Yes — 10+ OAuth providers |
| SSO (SAML 2.0 / OIDC) |
SAML 2.0 on Pro plan and above |
SAML 2.0 + OIDC on all plans (including free); managed enterprise IdP connections |
| MFA / TOTP |
TOTP free on all plans; SMS OTP MFA requires a paid plan |
TOTP, SMS OTP, WhatsApp OTP — all included |
| Fraud Protection |
Not built-in |
Bot protection, brute-force lockout, anomaly detection |
| Webhooks |
Database webhooks (via pg_net); limited auth events |
Dedicated auth event webhooks (login, signup, password change, etc.) |
| Self-hosting |
Yes — open-source, Docker-based |
Yes — open-source, Docker-based |
| Multi-tenant / B2B |
No built-in organisation model |
Built-in portal and role model for B2B multi-tenancy |
| Pricing model |
Free: 50K MAU. Pro: $25/mo includes 100K MAU, then usage-based overage |
Free: unlimited MAU. Paid plans start at $50/mo; auth-only pricing |
| Next.js App Router support |
Yes — via @supabase/ssr |
Yes — native @authgear/nextjs SDK |
Setup Comparison
Supabase Auth in Next.js
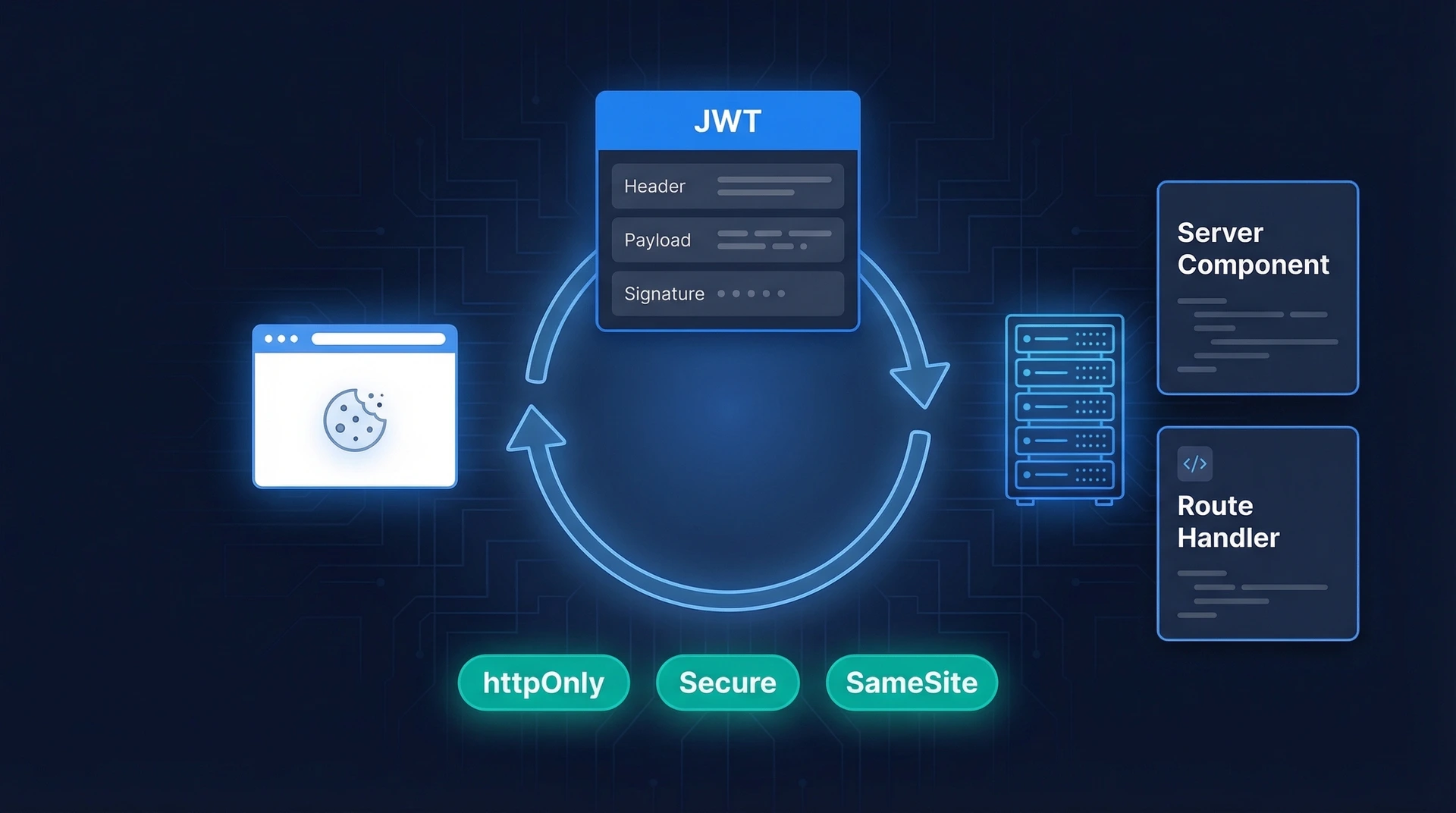
Supabase uses its @supabase/ssr helper package to handle cookie-based sessions in Server Components and middleware. You create two client variants — one for the browser, one for the server — and add a middleware to keep tokens refreshed.
1. Install packages
npm install @supabase/supabase-js @supabase/ssr
2. Add environment variables to .env.local:
NEXT_PUBLIC_SUPABASE_URL=https://your-project.supabase.co
NEXT_PUBLIC_SUPABASE_PUBLISHABLE_KEY=your-publishable-key
3. Create a server client utility (src/lib/supabase/server.ts):
import { createServerClient } from "@supabase/ssr";
import { cookies } from "next/headers";
export async function createClient() {
const cookieStore = await cookies();
return createServerClient(
process.env.NEXT_PUBLIC_SUPABASE_URL!,
process.env.NEXT_PUBLIC_SUPABASE_PUBLISHABLE_KEY!,
{
cookies: {
getAll() {
return cookieStore.getAll();
},
setAll(cookiesToSet) {
try {
cookiesToSet.forEach(({ name, value, options }) =>
cookieStore.set(name, value, options)
);
} catch {
// Safe to ignore in Server Components; middleware handles refresh
}
},
},
}
);
}
4. Protect a route using getClaims() — not getSession() — in server code. getClaims() validates the JWT signature against the project's published public keys on every call. getSession() does not revalidate the token and must not be used for access control on the server.
// src/app/dashboard/page.tsx
import { redirect } from "next/navigation";
import { createClient } from "@/lib/supabase/server";
export default async function DashboardPage() {
const supabase = await createClient();
const { data } = await supabase.auth.getClaims();
if (!data.claims) {
redirect("/login");
}
return Welcome, {data.claims.sub}
;
}
You also need a middleware file to refresh expired tokens on every request — see the Supabase Next.js server-side auth docs for the full middleware example.
Authgear in Next.js
Authgear ships a dedicated @authgear/nextjs SDK with first-class App Router support. Setup follows a catch-all route handler pattern — all auth callbacks (login, logout, token refresh) go through a single API route, and a currentUser() helper protects server-side pages.
1. Install the package
npm install @authgear/nextjs
2. Add environment variables to .env.local:
AUTHGEAR_ENDPOINT=https://your-project.authgear.cloud
AUTHGEAR_CLIENT_ID=your-client-id
AUTHGEAR_REDIRECT_URI=http://localhost:3000/api/auth/callback
SESSION_SECRET=a-random-string-of-at-least-32-characters
3. Create the shared config (src/lib/authgear.ts):
import type { AuthgearConfig } from "@authgear/nextjs";
export const authgearConfig: AuthgearConfig = {
endpoint: process.env.AUTHGEAR_ENDPOINT!,
clientID: process.env.AUTHGEAR_CLIENT_ID!,
redirectURI: process.env.AUTHGEAR_REDIRECT_URI!,
sessionSecret: process.env.SESSION_SECRET!,
};
4. Register the catch-all route handler (src/app/api/auth/[...authgear]/route.ts):
import { createAuthgearHandlers } from "@authgear/nextjs";
import { authgearConfig } from "@/lib/authgear";
export const { GET, POST } = createAuthgearHandlers(authgearConfig);
5. Protect a route using currentUser():
// src/app/dashboard/page.tsx
import { redirect } from "next/navigation";
import { currentUser } from "@authgear/nextjs/server";
import { authgearConfig } from "@/lib/authgear";
export default async function DashboardPage() {
const user = await currentUser(authgearConfig);
if (!user) {
redirect("/api/auth/login");
}
return Welcome, {user.sub}
;
}
Full step-by-step instructions are available in the Authgear Next.js quickstart guide.
Key Setup Differences
Both setups are comparable in complexity for a basic protected route. The main practical differences:
- Supabase requires two client utilities (browser and server) plus middleware. Authgear needs one config object and one route handler.
- Supabase sessions live in your Postgres instance. Authgear sessions are managed by the Authgear cloud service and verified server-side on each request.
- Supabase's security model is the database. Row Level Security policies in SQL control what each user can access. Authgear's security model is external to your database — you check
currentUser() and enforce access in your application logic.
When to Choose Supabase Auth
Supabase Auth is the right call when:
- You're already using Supabase for your database. There's no reason to add a separate auth service when auth is included in your existing Supabase plan. The RLS integration is genuinely excellent — being able to write
WHERE user_id = auth.uid() in SQL is powerful and clean.
- You're building a small-to-medium project that doesn't need advanced enterprise features. The free tier (50K MAU) covers most indie and startup use cases.
- You want tight Postgres integration. Supabase's auth is deeply woven into its database features. If your access control logic lives in the database, Supabase is a natural fit.
- You value the open-source, self-hostable stack. Supabase is open-source end-to-end. The entire platform can be self-hosted if you need data sovereignty without building auth separately.
- You don't need passkeys, advanced enterprise SSO, or fraud protection — or you're comfortable adding those separately if requirements grow.
When to Choose Authgear
Authgear is the stronger choice when:
- Authentication is the hard part of your product. If you're building a B2B SaaS, a fintech app, or anything where identity and access management is a first-class concern, a dedicated CIAM platform handles that complexity so your team doesn't have to.
- You need enterprise SSO. Authgear supports both SAML 2.0 and OIDC with managed IdP connections on all plans, including free. Supabase's SAML support requires the Pro plan or above.
- Passkeys are a priority. Authgear supports passkeys with dedicated flows, device sync, fallback methods, and an end-user account management portal. Supabase Auth does not currently support passkeys.
- You need fraud protection out of the box. Authgear includes bot protection, brute-force lockout, and anomaly detection. With Supabase, you'd need to build or integrate these separately.
- You're building multi-tenant B2B apps. Authgear has a built-in organisation and role model for B2B multi-tenancy. Supabase has no native organisation concept — you'd model that yourself in your database.
- You're not using Supabase's database. If you're on PlanetScale, Neon, or any other Postgres provider, there's no bundling benefit to Supabase Auth. A dedicated auth platform like Authgear gives you more flexibility.
- You want detailed auth event webhooks. Authgear fires webhooks for specific auth events (login, logout, signup, password change). Supabase's webhook system is database-level, not auth-event-level.
Conclusion
There's no universal winner here — both Supabase Auth and Authgear are well-engineered solutions that will handle authentication reliably for most Next.js applications.
The simplest way to decide: are you on Supabase? If yes, use Supabase Auth. The database integration, the RLS policies, and the all-in-one pricing make it the obvious choice for projects already in the Supabase ecosystem.
If you're not on Supabase, or if you need passkeys, enterprise SSO, fraud protection, or multi-tenant B2B capabilities, Authgear's specialisation pays off. You get a platform where the team's entire focus is on identity — and that shows in the breadth of features available without extra configuration.
Both are open-source and self-hostable if you need full control over your infrastructure. Authgear's free tier has no MAU cap — sign up and test it against your requirements before committing to a paid plan.
Frequently Asked Questions
Can I use Authgear with a Supabase database?
Yes. Authgear and Supabase are not mutually exclusive. You can use Authgear as your identity provider and Supabase as your database. Authgear issues standard JWTs, which you can verify in your API routes before querying Supabase. Authgear has published a guide on connecting Supabase with any auth provider, including how to mint Supabase-compatible tokens from external JWTs for RLS compatibility.
Does Supabase Auth work with Next.js App Router?
Yes. The @supabase/ssr package fully supports Next.js App Router, including Server Components, Route Handlers, and middleware. The older @supabase/auth-helpers-nextjs package is deprecated — use @supabase/ssr for any new project.
Is Authgear's Next.js SDK production-ready?
Yes. The @authgear/nextjs SDK supports the App Router natively, including server-side user retrieval via currentUser(), a catch-all route handler for auth callbacks, and client-side provider components. See the official Authgear Next.js quickstart for setup instructions and example code.