Authentication and authorization are the backbone of modern software. Every time a user logs in, calls an API, or performs a protected action, the system must verify who they are and what they're allowed to do. In distributed systems, these checks need to be not only secure but also fast and reliable.
OAuth 2.0 is a widely adopted framework that lets applications access user resources safely, without ever exposing passwords or credentials. Its flexibility and scalability make it ideal for web, mobile, and API-based systems, but misconfigurations or skipped safeguards can create serious security risks.
In this guide, we break down OAuth 2.0 security in practical terms. You'll learn how it works, what vulnerabilities to watch for, and best practices—covering PKCE, state parameters, token management, and more—to help you build secure, production-ready authorization systems.
Why OAuth 2.0 Security Matters
OAuth 2.0 enables clients to access resources on behalf of users or services without sharing passwords. It decouples authentication from authorization, enabling scalable integrations, microservices, and cross-platform applications.
However, OAuth’s flexibility introduces potential attack vectors. Without proper safeguards, attackers can:
- Intercept access tokens
- Forge authorization requests
- Gain unauthorized access to sensitive resources
Ensuring OAuth 2.0 flows are secure is therefore as critical as protecting passwords or API keys. Security decisions need to be deliberate, covering how tokens are issued, validated, transmitted, and revoked.
Understanding OAuth 2.0
OAuth 2.0 defines several roles and components:
- Resource Owner – The user who owns the data or resources
- Client – The application requesting access
- Authorization Server – Issues access tokens after authenticating the user
- Resource Server – Hosts the protected resources
Tokens are central to OAuth. The most common types are:
- Access Tokens – Short-lived tokens granting access to specific resources
- Refresh Tokens – Longer-lived tokens used to obtain new access tokens
OAuth flows vary depending on the client type (confidential vs. public) and the platform. For example:
- Authorization Code Flow – For server-side apps; uses an intermediate code exchanged for an access token
- Implicit Flow – For browser-based apps (now discouraged due to security concerns)
- Client Credentials Flow – For machine-to-machine communication
- Resource Owner Password Credentials Flow – Rarely recommended; involves passing credentials directly
Each flow has specific security considerations, and using the wrong flow in the wrong context can create vulnerabilities.
Core Security Requirements for OAuth 2.0
A secure OAuth implementation must satisfy several practical requirements:
- Tokens Must Be Valid and Unforgeable – Only the authorization server should be able to generate valid tokens.
- Flows Must Prevent CSRF and Replay Attacks – Mechanisms like state parameters prevent cross-site request forgery.
- Token Expiration Must Be Enforced – Short-lived tokens reduce exposure if compromised.
- Tokens Must Be Stored and Transmitted Securely – HTTPS and secure storage prevent interception.
- Revocation Must Be Supported – Users or admins should be able to invalidate tokens.
- Scopes Must Be Enforced – Tokens should only grant the minimum necessary access.
Failure to meet these requirements is a common source of OAuth security incidents.
Common OAuth 2.0 Vulnerabilities
Most security issues in OAuth arise from implementation mistakes rather than flaws in the protocol itself.
1. Missing or Weak PKCE
PKCE (Proof Key for Code Exchange) protects authorization code flows for public clients (like mobile apps) against interception attacks. Without PKCE, an attacker could capture an authorization code and exchange it for tokens.
2. State Parameter Mismanagement
The state parameter protects against cross-site request forgery (CSRF). If the parameter is missing, predictable, or poorly validated, attackers can trick users into authorizing unintended actions.
3. Long-Lived Access Tokens
Tokens that remain valid for extended periods increase risk. If stolen, an attacker can use them for a long time. Using short-lived access tokens with refresh tokens minimizes exposure.
4. Insecure Storage
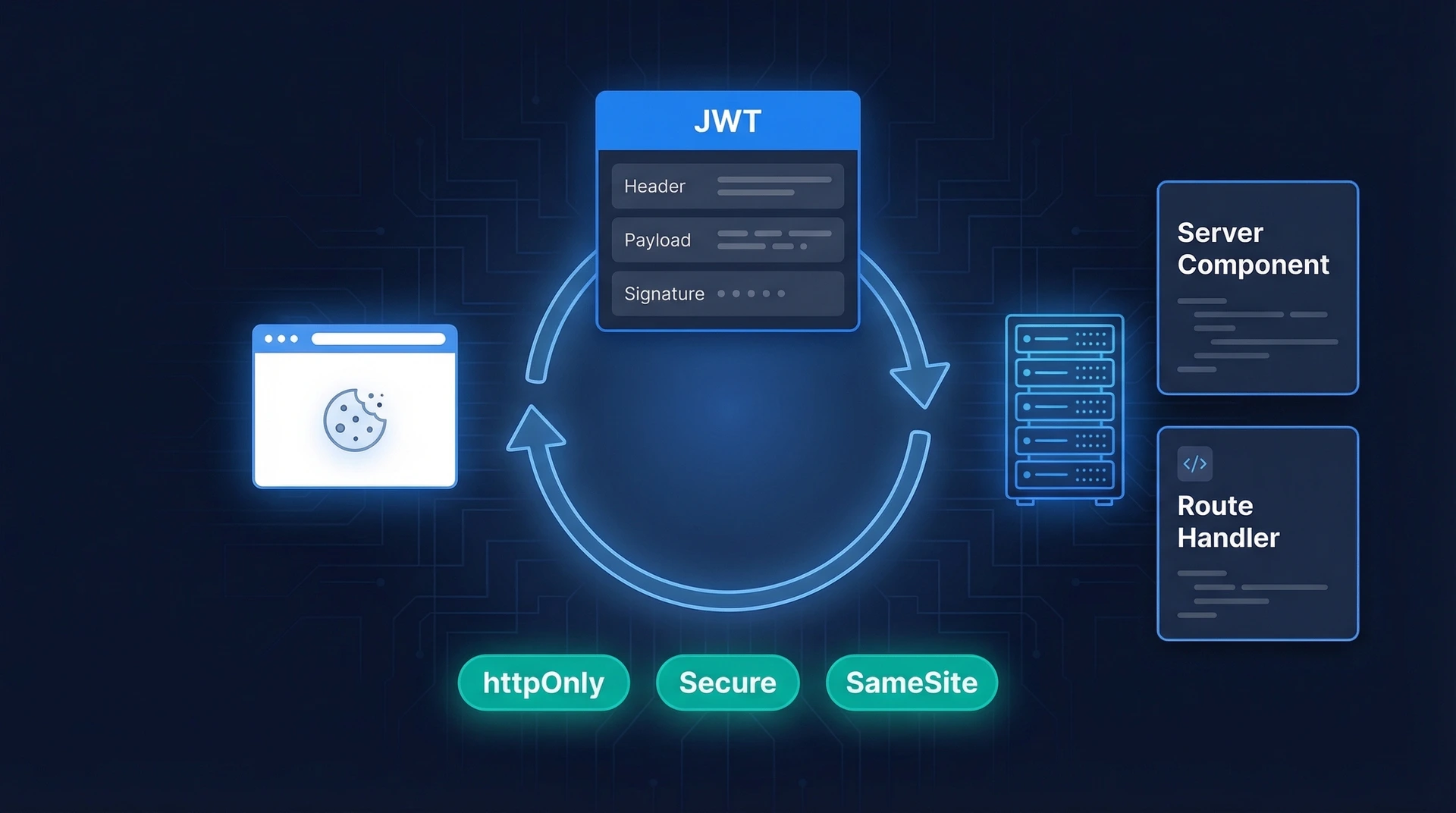
Tokens stored in local storage, unencrypted databases, or logs can be stolen. Web apps should use HTTP-only, secure cookies, while mobile apps should leverage secure device storage.
5. Inadequate Scope and Audience Validation
Access tokens must only allow operations and resources that were explicitly authorized. Failing to validate token scopes or audiences can let attackers access unintended resources.
6. Lack of Token Revocation
Without a revocation mechanism, compromised tokens remain valid until expiration. Systems handling sensitive data should provide revocation endpoints or token versioning.
OAuth 2.0 Security Best Practices
Following proven best practices helps teams mitigate common vulnerabilities and strengthen their OAuth implementation.
1. Always Use PKCE for Public Clients
PKCE prevents interception of authorization codes. It works by:
- Generating a random code verifier on the client
- Sending a hashed code challenge with the authorization request
- Validating the code challenge when exchanging the authorization code for tokens
PKCE is now required for most mobile and SPA clients.
2. Use Strong State Parameters
The state parameter should be:
- Randomly generated
- Unique per authorization request
- Verified on callback
This prevents CSRF attacks and ensures the response matches the request.
3. Short-Lived Access Tokens + Refresh Tokens
Short-lived tokens reduce risk if compromised. Refresh tokens should be used to obtain new access tokens securely and should have their own revocation and rotation mechanisms.
4. Secure Token Transmission
Tokens must always be transmitted over HTTPS to prevent interception. Mixed-content or unencrypted channels are a critical vulnerability.
5. Store Tokens Safely
Safe storage depends on the platform:
- Web apps – HTTP-only, Secure cookies
- Mobile apps – Encrypted keychains or secure storage APIs
- Server-side apps – Memory or protected configuration stores
Avoid exposing tokens to scripts or unprotected logs.
6. Validate Every Token
Tokens must be checked for:
- Signature validity
- Expiration time
- Audience and scope
- Issuer identity
Skipping any validation step can lead to unauthorized access.
7. Implement Token Revocation
Revocation mechanisms include:
- Token blacklists
- Token versioning (incrementing a version on sensitive account changes)
- Rotating signing keys
Revocation ensures compromised tokens can be invalidated before expiration.
8. Limit Sensitive Data in Tokens
Access tokens should include minimal information needed for authorization. Avoid embedding secrets, passwords, or sensitive personal data. If extra data is needed, consider encrypting the payload or fetching data from a secure backend.
9. Use Asymmetric Signing Where Appropriate
Tokens can be signed using symmetric (shared secret) or asymmetric (private/public key) methods. Asymmetric signing improves security in distributed environments:
- Private key signs tokens
- Public key validates tokens
- No secret is shared between services
This method simplifies key rotation and reduces exposure if a key is compromised.
10. Enforce Least Privilege via Scopes
Always define and enforce scopes to ensure tokens grant only the minimum necessary permissions. This limits damage in case a token is compromised.
Observability and Operational Benefits
OAuth 2.0 tokens can also support operational visibility:
- Trace requests across services
- Correlate user activity
- Identify unusual access patterns
- Debug authentication issues
Carefully designed token structures improve both security and maintainability.
When OAuth 2.0 Is the Right Choice
OAuth 2.0 is ideal for systems requiring:
- Delegated access to resources
- Distributed services or APIs
- Cross-platform clients
- Mobile or SPA applications
It is widely used for API authorization, single sign-on (SSO), and federated identity systems.
When OAuth 2.0 May Not Be Ideal
OAuth 2.0 might not be suitable if:
- Immediate token revocation is critical
- Strict centralized control is required
- Token size must remain minimal
- Legacy or simple applications don’t need delegated authorization
In these cases, traditional session-based authentication or proprietary protocols may be simpler and safer.
Designing Secure OAuth 2.0 Systems
Security should be considered from the very start of your system design, not added as an afterthought. OAuth 2.0 may handle token issuance and access delegation, but the overall safety of your implementation depends on decisions made across architecture, infrastructure, and operations.
Before building or scaling your system, teams should carefully evaluate:
- Threat models for each flow – Understand the types of attacks your app could face, such as token interception, CSRF, or replay attacks. Mapping these threats early helps you design flows that resist them.
- Compliance requirements – Regulations like GDPR, HIPAA, or industry-specific rules may dictate how tokens are stored, transmitted, or revoked. Aligning with compliance ensures both security and legal safety.
- Infrastructure scale and complexity – Systems that operate across multiple services, regions, or clients require stricter key management, monitoring, and token validation strategies.
- Operational maturity – Consider whether your team has the monitoring, logging, and revocation capabilities to respond to suspicious token activity or breaches quickly.
By planning these aspects ahead of time, you reduce the risk of introducing vulnerabilities as your system grows and becomes more complex. Security becomes a built-in part of the architecture rather than a patch applied later.
Practical OAuth Security Checklist
Use this checklist to validate your OAuth implementation:
- PKCE is implemented for public clients
- State parameters are used and validated
- Tokens are short-lived; refresh tokens are handled securely
- HTTPS is enforced for all requests
- Tokens are stored safely
- Scope and audience are validated
- Revocation mechanisms exist and are tested
- Sensitive data is not included in tokens
- Signing keys are rotated regularly
- Logs and monitoring capture suspicious token activity
Adhering to this checklist reduces the likelihood of OAuth-related security incidents.
Bottom Line
OAuth 2.0 is a flexible and powerful framework for modern authorization. When implemented correctly, it enables apps to grant secure, delegated access without ever exposing user credentials.
Most security issues don’t come from OAuth itself—they arise from gaps in implementation, such as missing PKCE, weak state handling, long-lived tokens, insecure storage, or incomplete validations. Applying best practices like short-lived tokens, PKCE, strong state parameters, revocation strategies, and robust signing significantly reduces risk.
Security should be a deliberate part of your system design. Thoughtful architecture, careful implementation, and ongoing operational practices ensure OAuth flows remain reliable, scalable, and secure as your system grows.
For teams looking to implement OAuth 2.0 safely and confidently, Authgear provides production-ready tools for secure token management, flow validation, and operational visibility.
Get started with Authgear today to simplify OAuth adoption, enforce best practices, and scale your authorization systems safely from day one.
FAQs
What is the biggest OAuth 2.0 security risk?
Improper flow implementation, especially missing PKCE or unvalidated state, can allow attackers to intercept authorization codes or tokens.
Are OAuth 2.0 tokens secure by default?
Tokens are secure only when flows are implemented correctly, with strong signing, proper validation, and secure storage. Weak implementations introduce vulnerabilities.
Should sensitive data be included in tokens?
No. Tokens should include only the minimum required information. Sensitive data should remain on secure backend systems.
How often should signing keys or secrets be rotated?
Keys should be rotated regularly based on risk and security policy. Rotation limits exposure if a key is compromised and is considered standard practice.