FIDO2 is an open authentication standard that lets users sign in to websites and apps without passwords. Instead of typing a password, FIDO2 authentication verifies identity through a trusted device — a smartphone, laptop, or FIDO2 security key — using public-key cryptography. The private key stays on the device, so there is nothing for attackers to phish or steal from a server.
Developed by the FIDO Alliance and the W3C, FIDO2 combines two specifications: WebAuthn (the browser API) and CTAP (the protocol that talks to authenticators). Together they enable passwordless authentication across every major browser and operating system.
This guide explains what FIDO2 is, how FIDO2 authentication works, how it compares to older standards like FIDO U2F, and how passkeys build on top of it.
Understanding What Is FIDO2
To clearly understand what is FIDO2, it is useful to start with its purpose. FIDO2 was created to replace passwords with secure authentication mechanisms based on cryptographic technology.
In traditional authentication systems, users share a password with the server. The server stores this credential and compares it during future login attempts. If attackers gain access to stored password data or trick users into revealing their credentials, they can compromise accounts.
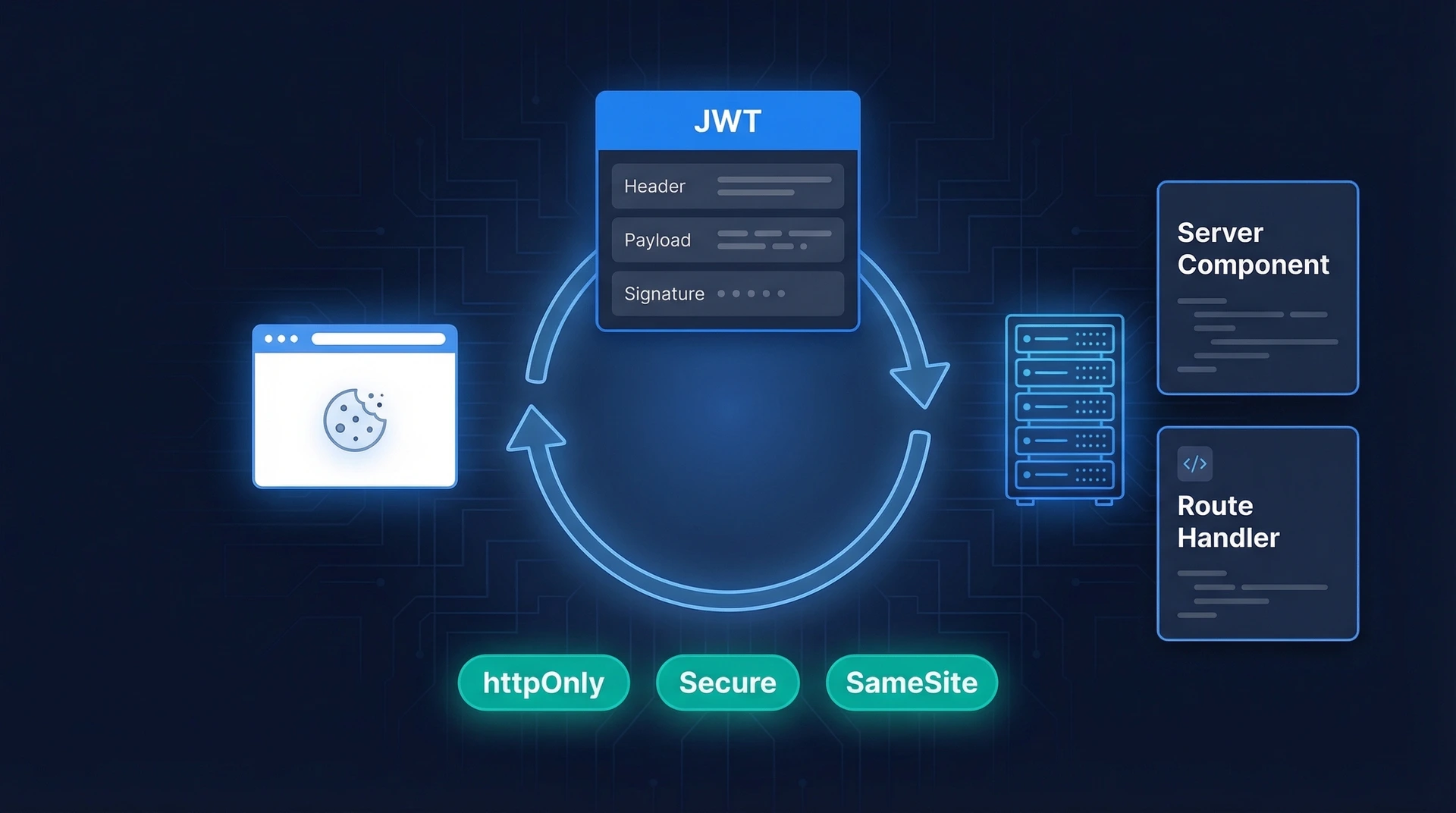
FIDO2 authentication eliminates this risk by replacing passwords with cryptographic keys. When a user registers with a service that supports FIDO login, their device generates a pair of keys. One key is public and stored by the service, while the other key is private and securely stored on the user's device.
During authentication, the service sends a challenge to the user's device. The device signs this challenge using the private key and returns the result. The server verifies the response using the public key. Because the private key never leaves the device, it cannot be intercepted or stolen.
In simple terms, when people ask what is FIDO authentication, the answer is that it is a method of verifying identity using cryptographic credentials tied to a user's device rather than a password.
This approach improves both security and usability. Users no longer need to remember complex passwords, and organizations no longer need to store sensitive credentials.
Why the Industry Is Moving Toward FIDO Authentication
Understanding what is FIDO authentication also requires understanding the limitations of password-based security. Passwords have several well-known weaknesses. One of the most common problems is password reuse. Because users maintain many accounts, they often reuse the same credentials across different services. If one service suffers a data breach, attackers can attempt to use those credentials on other platforms.
Phishing attacks present another major risk. Attackers create fake websites that resemble legitimate login pages. When users enter their credentials, the attackers capture the information and use it to access real accounts.
Even strong password policies cannot eliminate these risks entirely. As a result, organizations continue to invest significant resources in monitoring authentication activity and protecting stored password data.
FIDO2 authentication addresses these challenges by removing passwords from the login process. Instead of relying on shared secrets, FIDO login verifies identity using cryptographic keys stored on trusted devices.
This change significantly reduces the risk of credential theft. Since there is no password to capture, phishing attacks become far less effective. In addition, FIDO2 authentication improves the user experience by allowing login through biometrics or device confirmation rather than manual password entry.
These advantages explain why many organizations are adopting FIDO login as part of their long-term authentication strategy.
How FIDO2 Authentication Works
To fully understand what FIDO2 is, it is important to examine how FIDO2 authentication functions in practice. The authentication process typically includes two stages: registration and authentication.
Registration
Registration creates the foundation for secure FIDO2 authentication. This process is sometimes referred to as credential enrollment because it registers a trusted device that can later be used for FIDO login.
During registration, the user chooses to enable FIDO login on a supported browser, application, or platform. The service then sends a registration request to the browser through the WebAuthn interface. The browser communicates with the user's device authenticator and prompts the user to verify their identity before continuing with the setup.
This verification step usually involves device-based authentication methods. In most modern devices, this includes biometric verification such as fingerprint scanning, facial recognition, or other built-in biometric sensors. Some systems also allow authentication using a secure device PIN that is stored locally on the device. This ensures that only the legitimate user can approve the registration process.
Once the user confirms their identity, the device generates a unique pair of cryptographic keys. The public key is securely transmitted to the service and stored with the user's account on the server. The private key, which is used to verify future login attempts, remains securely stored within the device and never leaves it.
This registration process completes the setup required for FIDO2 authentication, enabling the user to securely sign in without relying on traditional passwords.
Authentication
After registration is complete, the user can perform FIDO login whenever they need to access their account.
When the user initiates login, the server generates a cryptographic challenge. This challenge is sent to the browser, which forwards it to the authentication device.
The device prompts the user to confirm their identity using biometrics or device unlock. Once verified, the device signs the challenge using the private key.
The signed response is sent back to the server, which verifies the signature using the stored public key. If the verification succeeds, the user is authenticated.
Because the private key never leaves the device, FIDO2 authentication protects against many common attack methods.
Core Technologies Behind FIDO2: WebAuthn and CTAP
Two key technologies make FIDO2 authentication possible across browsers, devices, and applications.
WebAuthn
Web Authentication, commonly known as WebAuthn, is the web standard that allows websites to interact with authentication devices as part of FIDO2 authentication. Developed by the W3C in collaboration with the FIDO Alliance, WebAuthn provides a secure interface that enables browsers to support FIDO login directly within web applications.
WebAuthn defines how a website sends authentication or registration requests to the user's browser and how the browser communicates with authenticators such as smartphones, laptops, or hardware security keys. The browser acts as a secure intermediary, passing cryptographic challenges to the authenticator and returning signed responses back to the website.
Because of this structure, sensitive credentials like private keys never leave the user's device. This design helps protect FIDO authentication from phishing, credential theft, and server-side data breaches.
CTAP
The Client to Authenticator Protocol, known as CTAP, handles the communication between the client platform (a browser or operating system) and the authenticator device used in FIDO2 authentication. While WebAuthn defines how websites send authentication requests to the browser, CTAP defines the next leg of the journey: how the browser talks to authenticators such as hardware security keys, smartphones, or built-in biometric sensors.
Through CTAP, the browser sends cryptographic challenges to the authenticator and receives signed responses that confirm the user's identity during FIDO login. This protocol ensures that the authentication device can safely generate and use cryptographic keys without exposing sensitive information. CTAP has evolved through two versions: CTAP1 (essentially the legacy FIDO U2F protocol) and CTAP2, which enables the passwordless flows that define modern FIDO2 authentication.
By working together, WebAuthn and CTAP create the technical foundation that powers FIDO authentication, enabling secure, passwordless login experiences across browsers, platforms, and devices.
Types of Authenticators Used in FIDO Login
Different types of authenticators support FIDO login, depending on how credentials are stored and how users interact with them.
Platform Authenticators
Platform authenticators are authentication mechanisms built directly into devices such as smartphones, laptops, and tablets. These authenticators are integrated into the device's operating system and hardware, allowing users to complete FIDO login using features that are already available on their devices.
Common examples include fingerprint sensors, facial recognition systems, and secure hardware modules such as Trusted Platform Modules (TPM) or secure enclaves. When a user initiates FIDO2 authentication, the device prompts them to verify their identity through these built-in methods before allowing the login request to proceed.
Because the cryptographic keys used in FIDO authentication are stored securely within the device, sensitive credentials are protected from external access. Platform authenticators provide a highly convenient experience since users do not need to carry additional hardware while still benefiting from strong, device-based security.
Roaming Authenticators and FIDO2 Security Keys
Roaming authenticators are external authentication devices that users can carry and use across multiple systems and platforms. Unlike platform authenticators that are built into a specific device, roaming authenticators are portable and can be connected to different computers, smartphones, or tablets when performing FIDO login.
These devices typically connect through USB, NFC, or Bluetooth Low Energy (BLE). Newer versions of the CTAP specification also support a hybrid transport (sometimes called caBLE), which lets users scan a QR code on a computer and authenticate from their phone. This flexibility allows users to authenticate securely regardless of the device they are using. Hardware security keys are one of the most common examples of roaming authenticators used in FIDO2 authentication. When a login request is initiated, the user simply connects the key and confirms the authentication action, often by tapping the device.
Roaming authenticators are widely used in enterprise environments where organizations require stronger authentication controls. They provide an additional layer of protection for FIDO authentication, especially for administrators, remote employees, and users who need secure access across multiple systems.
FIDO vs FIDO2: What Changed
The FIDO Alliance has released several standards over the years. Understanding the difference between FIDO and FIDO2 helps clarify the current landscape.
The original FIDO specifications included two protocols: FIDO UAF (Universal Authentication Framework), which supported passwordless login on mobile devices, and FIDO U2F (Universal Second Factor), which added a hardware security key as a second factor on top of passwords. Both improved security, but they had limitations. UAF required platform-specific integration, and U2F still depended on passwords as the primary factor.
FIDO2 is the successor that unifies and extends both. By combining WebAuthn and CTAP2, FIDO2 authentication supports passwordless, second-factor, and multi-factor login through a single web standard that works natively in browsers. No plugins, no platform-specific code.
FIDO2 vs FIDO U2F Comparison
For organizations still using FIDO U2F security keys, the good news is that CTAP1 provides backward compatibility. Existing U2F keys continue to work as second-factor authenticators within the FIDO2 framework.
How Passkeys Relate to FIDO2
Passkeys are one of the most widely discussed innovations related to FIDO2 authentication. A passkey is essentially a user-friendly implementation of FIDO credentials. Passkeys rely on the same cryptographic principles used in FIDO2 authentication, but they simplify the user experience.
There are two types of passkeys. Synced passkeys allow credentials to be securely stored and synchronized across devices through platform ecosystems such as iCloud Keychain, Google Password Manager, or Microsoft accounts. This means a passkey created on an iPhone is also available on a Mac or iPad signed into the same Apple account. Device-bound passkeys, on the other hand, are tied to a specific piece of hardware such as a YubiKey or a device's TPM and cannot be copied or synced.
When users perform FIDO login using passkeys, the process remains based on cryptographic authentication. However, the experience is designed to feel more seamless, especially with synced passkeys that work across multiple devices without re-enrollment.
Because passkeys are built on the FIDO2 authentication standard, they represent an important step toward widespread passwordless adoption.
Implementing FIDO Login in Applications
Organizations interested in deploying FIDO login must design authentication systems that support WebAuthn and compatible authenticators.
The first step in implementation is enabling WebAuthn support within the application's authentication flow. Developers must design registration processes that allow users to register authentication devices securely.
During this process, users should be guided through setting up their device for FIDO2 authentication. Clear instructions help ensure successful enrollment.
Organizations should also allow users to register multiple authenticators. This ensures that users can still access their accounts if their primary device becomes unavailable.
Account recovery processes must also be carefully designed. If users lose access to their device, the system must provide secure ways to restore access without compromising security. Proper implementation ensures that FIDO login remains both secure and convenient.
Security Benefits of FIDO2 Authentication
The adoption of FIDO2 authentication offers several important security advantages. One major benefit is resistance to phishing attacks. Because authentication credentials are linked to specific domains, fraudulent websites cannot request valid authentication responses.
Another advantage is the elimination of password storage. Since servers store only public keys, there are no sensitive credentials for attackers to steal in the event of a database breach.
FIDO login also protects against credential reuse because each service receives a unique cryptographic key pair.
These protections make FIDO2 authentication one of the most secure authentication methods available today.
Business and User Experience Benefits
Beyond security improvements, FIDO2 authentication also delivers operational and usability benefits.
First, passwordless authentication significantly reduces password reset requests. This lowers support costs and improves operational efficiency.
Second, FIDO login simplifies the user experience. Users can authenticate quickly using biometrics or device confirmation rather than typing complex passwords.
Third, stronger authentication improves trust in digital platforms. Users feel more confident when their accounts are protected by modern security technologies.
These benefits explain why many organizations are actively exploring FIDO2 authentication as part of their identity strategy.
The Future of FIDO Authentication
As digital ecosystems continue to evolve, authentication methods must adapt to new security challenges and rising user expectations. Cyber threats such as phishing, credential stuffing, and large-scale data breaches have exposed the weaknesses of password-based systems. As a result, organizations are actively exploring stronger and more user-friendly alternatives. The growing adoption of FIDO2 authentication suggests that passwordless login will play an increasingly important role in the future of digital identity.
Major browsers, operating systems, and authentication frameworks now support the standards required for FIDO authentication, making it easier for organizations to integrate secure login experiences into their applications. Developers can implement these capabilities through standard APIs, reducing the complexity that traditionally came with advanced authentication systems.
At the same time, users are becoming more familiar with device-based verification methods. Many people already unlock their smartphones using fingerprints, facial recognition, or device PINs. FIDO2 authentication extends these familiar interactions to online services, allowing users to verify their identity in a fast and intuitive way without needing to remember or manage passwords.
Another important development is the growing adoption of passkeys, which are built on the same principles as FIDO authentication. Passkeys allow users to sign in across devices using cryptographic credentials that are securely synchronized through trusted ecosystems. This further strengthens the role of FIDO login as a foundation for modern passwordless authentication.
As these technologies continue to mature, the reliance on traditional passwords is expected to decline significantly. For organizations planning the next generation of secure digital services, understanding what is FIDO2 and how FIDO2 authentication works is becoming an essential step toward building safer and more scalable identity systems.
Bottom Line
FIDO2 replaces passwords with cryptographic credentials stored on trusted devices. This eliminates the risks of phishing, credential stuffing, and server-side password breaches while giving users a faster login experience through biometrics or security keys.
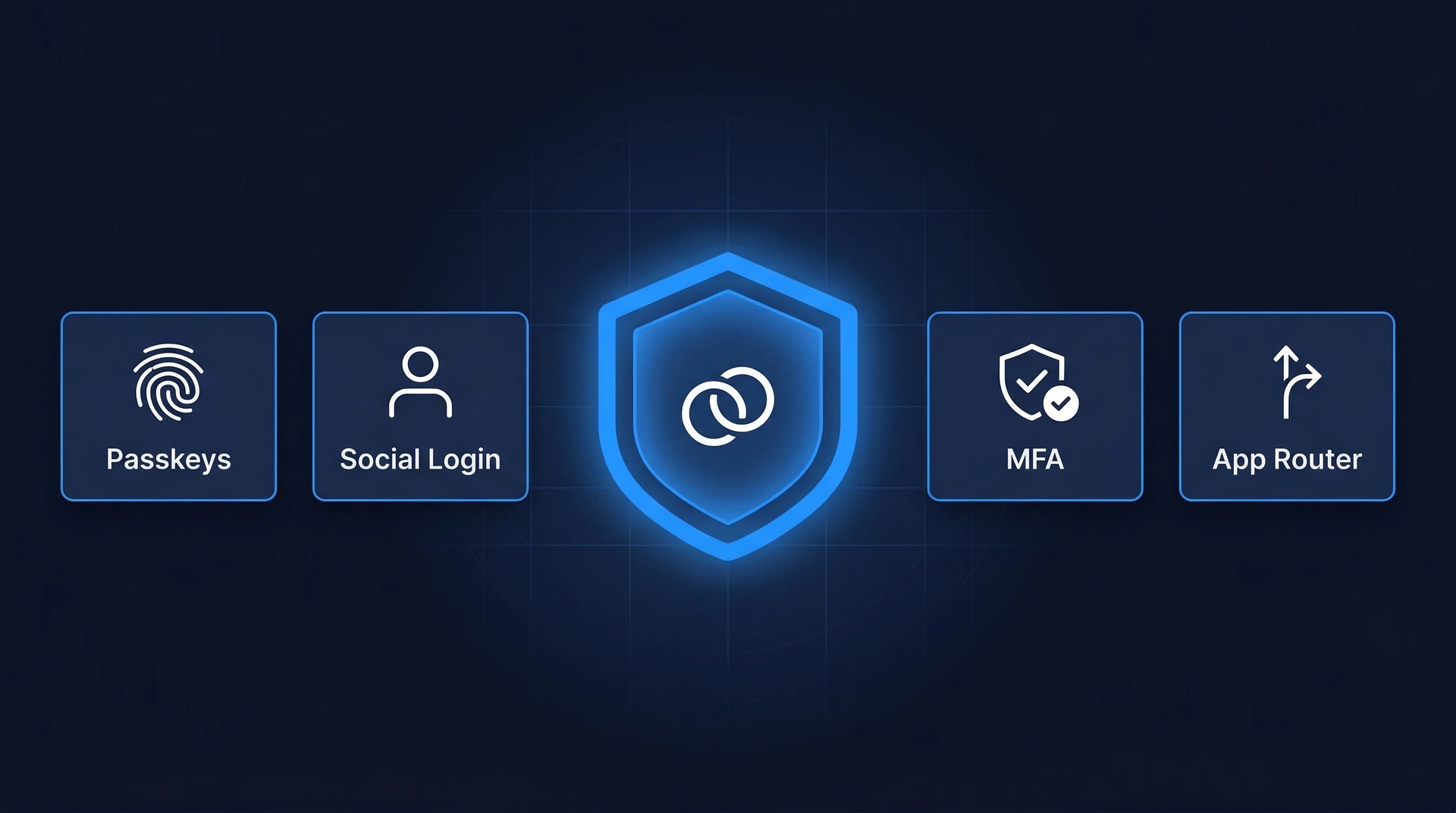
For development teams evaluating passwordless authentication, Authgear provides built-in support for passkeys and FIDO2 security keys alongside other user authentication methods like TOTP, SMS OTP, and social login. You can add FIDO2 authentication to your app without building the WebAuthn integration from scratch.
Get started with Authgear to add passwordless login to your application.
FAQs
What is FIDO2?
FIDO2 is an open authentication standard developed by the FIDO Alliance and the W3C. It allows users to sign in to websites and applications without passwords by using a trusted device such as a smartphone, laptop, or FIDO2 security key. FIDO2 is made up of two components: WebAuthn (the browser API) and CTAP (the authenticator protocol).
What is FIDO authentication?
FIDO authentication is a passwordless method of verifying users based on standards from the FIDO Alliance. Instead of entering a username and password, users complete login through a device-based method such as fingerprint recognition, facial recognition, or a hardware security key. The term covers both the original FIDO UAF/U2F standards and the newer FIDO2 standard.
How does FIDO2 work?
During registration, the user's device generates a public-private key pair. The public key is stored on the server; the private key stays on the device. At login, the server sends a cryptographic challenge, the device signs it with the private key, and the server verifies the signature with the public key. Because the private key never leaves the device, there is nothing to phish or steal.
What is a FIDO2 security key?
A FIDO2 security key is a small hardware device — typically a USB, NFC, or Bluetooth dongle — that stores cryptographic credentials and performs FIDO2 authentication. Popular examples include the YubiKey 5 series, Google Titan Key, and Thetis Pro. Security keys are roaming authenticators: they work across multiple computers and phones.
What is the difference between FIDO and FIDO2?
FIDO refers to the original set of standards (FIDO UAF and FIDO U2F) released before 2018. FIDO2 is the successor that combines WebAuthn and CTAP2 into a single browser-native standard. The main upgrade is that FIDO2 supports fully passwordless login, while the original FIDO U2F only worked as a second factor alongside a password.
How is FIDO2 related to passkeys?
Passkeys are the user-facing name for FIDO2 credentials. They use the same WebAuthn/CTAP2 technology under the hood. The key difference is that synced passkeys can be backed up and synchronized across devices through iCloud Keychain, Google Password Manager, or similar platform services, while device-bound passkeys (like those on a YubiKey) stay on one device.
Is FIDO2 authentication secure?
Yes. FIDO2 authentication is phishing-resistant because credentials are cryptographically bound to the website's domain — a fake site cannot trigger a valid response. Servers store only public keys, so a database breach does not expose usable credentials. Each service gets a unique key pair, preventing credential reuse across sites.